特色内容
亚洲必赢研究:控制器编程方法,建议
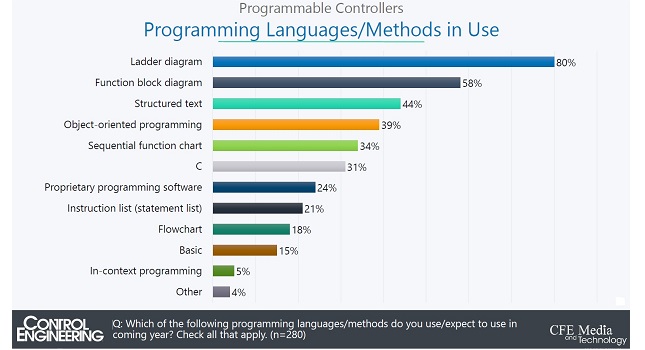
必赢亚&亚洲必赢#27954;平台控制工程2020工业可编程控制器的研究表明,梯形逻辑继续主导编程,软件集成和仿真能力不断增强,受访者寻求编程灵活性。参见自2018年以来的6个软件相关可编程控制器的变化和9个可编程控制器的软件建议。
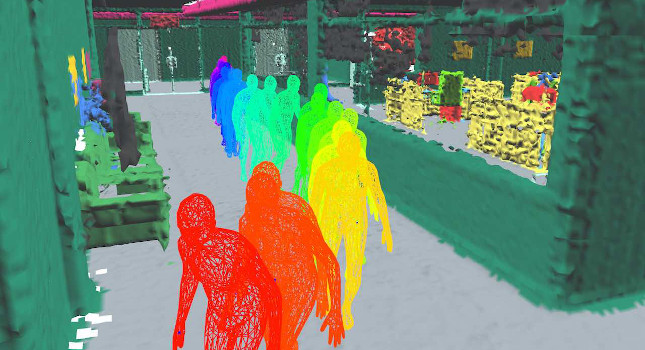
亚洲必赢研究人员给予机器人类似人类的感知他们的物理环境
麻省理工亚洲必赢学院的研究人员为机器人开发了一种名为3D动态场景图的空间感知表示,它可以使机器人在工厂车间或其他危险环境中与人合作。
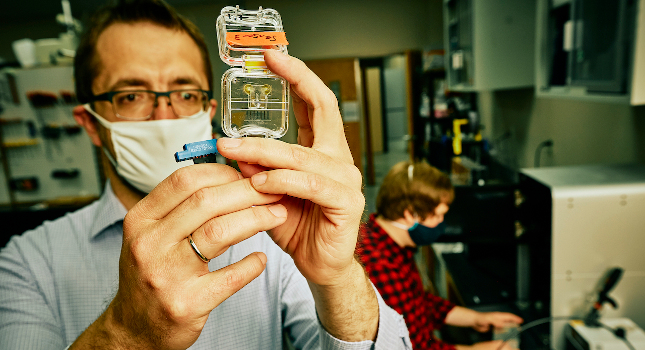
亚洲必赢研究人员利用3D打印技术为微流体打开了一扇新的大门
蒙大拿州立大学的研究人员已经开发出使用3D打印制作亚洲必赢的微流控芯片,从而降低制造时间的设备的新方法,并可能允许研究人员制造设备的实惠,定制的原型。
确保远程访问的生存和发展
安全远程访问(SRA)被用来帮助企业生存和COVID-19大流行期间发展起来的,但也有一些新的挑战需要加以考虑。请参阅第10种远程访问的最佳做法。
亚洲必赢研究:控制器编程方法,建议
必赢亚&亚洲必赢#27954;平台控制工程2020工业可编程控制器的研究表明,梯形逻辑继续主导编程,软件集成和仿真能力不断增强,受访者寻求编程灵活性。参见自2018年以来的6个软件相关可编程控制器的变化和9个可编程控制器的软件建议。
企业联合起来,加快产业转型
西门子和SAP宣布建立合作伙伴关系,旨在为产品生命周期、供应链和资产管理应用程序提供互补的软件解决方案。
石墨烯屏蔽提高了废水保护能力
赖斯大学的研究人员发现,石墨烯的亚洲必赢屏蔽有助于颗粒破坏抗生素耐药性细菌和自由浮动的抗生素抗性基因和其他潜在的超级细菌在污水处理厂。